Quantum is touted as more revolutionary technology than even modern day internet. Quantum computers will provide unparalleled processing power and run billion times faster than any supercomputer ever made. The principles of nature and quantum physics will enable quantum computers to bring the expected revolution to the world in a decade or two. However, there are good and not so good uses of any technology and quantum is no different. The same advantages, for instance, can enable breaking of security at any level of cyber infrastructure. Quantum computers bring major challenges to cyber security and need to develop mechanisms to counter the threat. In this article, Quantum Guru touches upon the highly decorated Quantum Key Distribution to help alleviate the risk.
What are the cybersecurity risks to current cryptographic techniques?
Current cybersecurity infrastructure mandates following two functions:
- Authentication – Allows distant users to trust their counterpart and validate the content of their exchanges. Public key scheme is used to implement authentication
- Confidentiality – Allows (and is required for) exchange of any private information between distant users. It is executed in a two-step process and users have to share a secret key at the start. It uses the public-key protocol, commonly known as the key exchange mechanism. The secret key is used in a symmetric key encryption scheme.
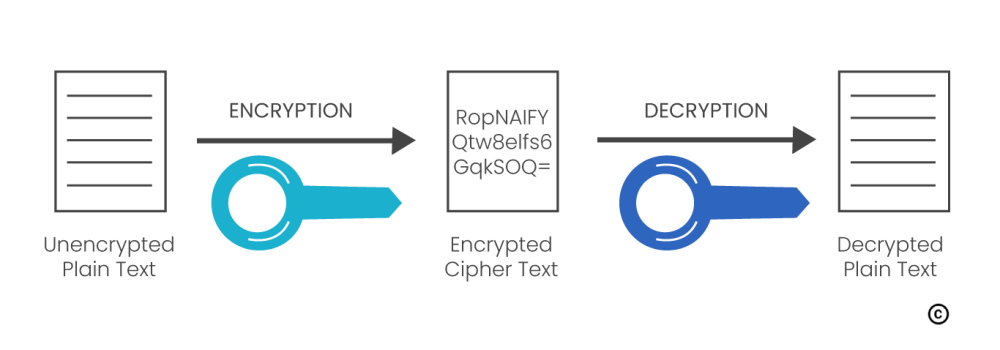
Therefore, both functions depend on similar cryptographic techniques, known as asymmetric or public-key cryptography as shown in Figure 1.
However, cybersecurity is much more than the underlying cryptography. All current hacks and security failures do not come from weak cryptography, but rather from faulty implementation, social engineering, to name a few. Current systems trust the cryptography and fight to get the implementation right.
Unfortunately, things are about to change with the advent of quantum computers. Today the point of cryptographic vulnerability is public-key cryptography that is implemented using algorithms such as RSA. These are used both to authenticate data and to securely exchange data encryption keys.
The processing power of the quantum computer can solve these mathematical problems exponentially faster than classical computers and break public-key cryptography. As a result, the currently used public-key cryptosystems are not appropriate to secure data that require long-term confidentiality. An adversary could indeed record encrypted data and wait until a quantum computer is available to decrypt it, by attacking the public keys.
What is Quantum Key Distribution (QKD)?
The concept of QKD was first proposed in 1970’s. QKD is the only provable secure communication method because it uses physics, not math to encrypt data. QKD also known as Quantum Cryptography is a technology that uses quantum physics aimed to secure the distribution of symmetric encryption keys. QKD is the technology that can address a long-term confidentiality issue of secured data.
How does QKD improve traditional cryptography implementations?
A security solution is as secure as its weakest link and in network encryption, the current weakest link with respect to the quantum computer threat is the secret key distribution based on public key cryptography. As its name suggests, QKD is used to distribute encryption keys whose security is based on quantum physics and is thus guaranteed for the long-term.
How does QKD work?
QKD transmits photons, which are “quantum particles” of light across an optical link. The principles of quantum physics stipulate that observation of a quantum state causes perturbation. The various QKD protocols are designed to ensure that any attempt by an eavesdropper to observe the transmitted photons will indeed perturb or disturb the transmission.This disturbance will lead to transmission errors, which can be detected by the legitimate users. This is used to verify the security of the distributed keys.
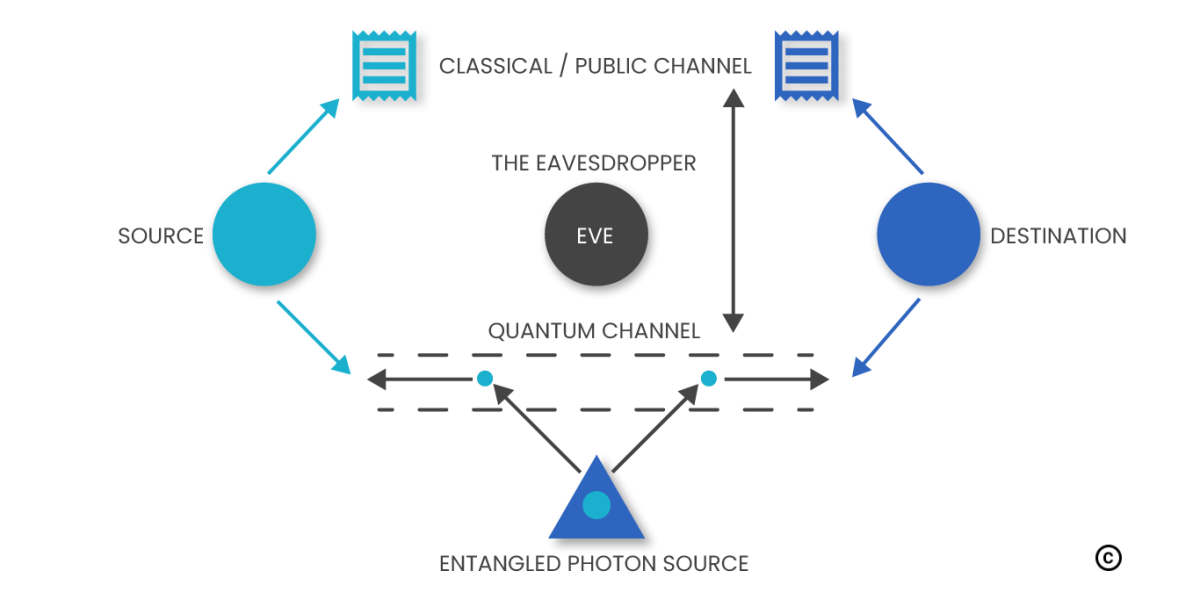
QKD implementation requires interactions between the legitimate users. These interactions need to be authenticated that are achieved through various cryptographic means. As a result, QKD can utilize an authenticated communication channel and transform it into a secure communication channel as shown in figure 2.
In theory, QKD should be combined with One-Time Pad (OTP) encryption to achieve provable security. However, an OTP requires keys, which are as long as the data to be encrypted,= and can be used only once. This would impose strong limitations on the available bandwidth as the key distribution rate of QKD is typically 1’000 to 10’000 times lower than conventional optical communications. Therefore, in practice, QKD is often combined with conventional symmetric encryption, such as AES, and used to frequently refresh short encryption keys. This is sufficient to provide quantum-safe security.
What is the need to implement quantum-safe cryptography?
The greatest threat to public cryptography is asymmetric algorithms used for digital signatures and key exchange. There are already quantum algorithms, such as the famous Shor algorithm, which can break RSA and Elliptic Curve algorithms once a universal quantum computer is available. Another famous quantum algorithm, the Grover algorithm, attacks symmetric cryptography. Fortunately, Grover’s risk can be countered by a simple expansion of the key size. For example, AES symmetric encryption scheme with 256 bit keys is considered as quantum-safe. Although certain theory estimates, a quantum computer with 4099 perfectly stable qubits could break the RSA-2048 encryption in 10 seconds (instead of 300 trillion years).
Countering the quantum computer threat will rely on following two pillars:
- Post-Quantum algorithms – Development of new classical algorithms, which should resist adverse usage of quantum computer
- QKD – Provide quantum-safe key exchange based on very quantum principles. Fortunately, it is available today.
Does Quantum Key Distribution offer absolute security?
1. It must be based on sound principles
2. Its implementation must be full proof and susceptible to vulnerabilities
Contrary to classical key distribution techniques, which rely on unproven assumptions and thus do not fulfil the first criterion, the security of QKD is based on the laws of quantum physics and can be rigorously proven. Having said that, it is imperative that the practical embodiment of a QKD system also fulfils the second criterion and does not have any implementation flaws. All the announcements about QKD having been hacked were related to implementation flaws. The flaws though serious are inherent to any technological system and are rectified as technology matures. In summary, the security of QKD is based on sound principles and, if properly implemented, =guarantees absolute security for key distribution.



Hello.This post was really interesting, particularly because I was looking for thoughts on this subject last Wednesday.